Search
Search for projects by name
 Astar zkEVM
Astar zkEVM
Badges
About
Astar zkEVM is a Validium that leverages Polygon's CDK and zero-knowledge cryptography to enable off-chain transactions while maintaining EVM equivalence.
Badges
About
Astar zkEVM is a Validium that leverages Polygon's CDK and zero-knowledge cryptography to enable off-chain transactions while maintaining EVM equivalence.
Why is the project listed in others?
Consequence: projects without a sufficiently decentralized data availability committee rely on few entities to safely attest data availability on Ethereum. A small set of entities can collude with the proposer to finalize an unavailable state, which can cause loss of funds.
Learn more about the recategorisation here.
Astar zkEVM Launch
2024 Mar 6th
Astar Network launched Astar zkEVM, integrated with Polygon Agglayer.
Funds can be stolen if
Funds can be lost if
Funds can be frozen if
Users can be censored if
MEV can be extracted if
There is no mechanism to have transactions be included if the sequencer is down or censoring. Although the functionality exists in the code, it is currently disabled.
STARKs and SNARKs are zero knowledge proofs that ensure state correctness. STARKs proofs are wrapped in SNARKs proofs for efficiency. SNARKs require a trusted setup.
Proof construction relies fully on data that is NOT published onchain. There exists a Data Availability Committee (DAC) with a threshold of 3/5 that is tasked with protecting and supplying the data.
Even though there is a 3d Timelock for upgrades, forced transactions are disabled.
Only the whitelisted proposers can publish state roots on L1, so in the event of failure the withdrawals are frozen.
Set of parties responsible for signing and attesting to the availability of data.
There are no onchain assets at risk of being slashed in case of a data withholding attack, and the committee members are not publicly known.
There is no fraud detection mechanism in place. A data withholding attack can only be detected by nodes downloading the full data from the DA layer.
The committee does not meet basic security standards, either due to insufficient size, lack of member diversity, or poorly defined threshold parameters. The system lacks an effective DA bridge and it is reliant on the assumption of an honest sequencer, creating significant risks to data integrity and availability.
There is no delay in the upgradeability of the bridge. Users have no time to exit the system before the bridge implementation update is completed.
The relayer role is permissioned, and the DA bridge does not have a Security Council or a governance mechanism to propose new relayers. In case of relayer failure, the DA bridge will halt and be unable to recover without the intervention of a centralized entity.
Architecture

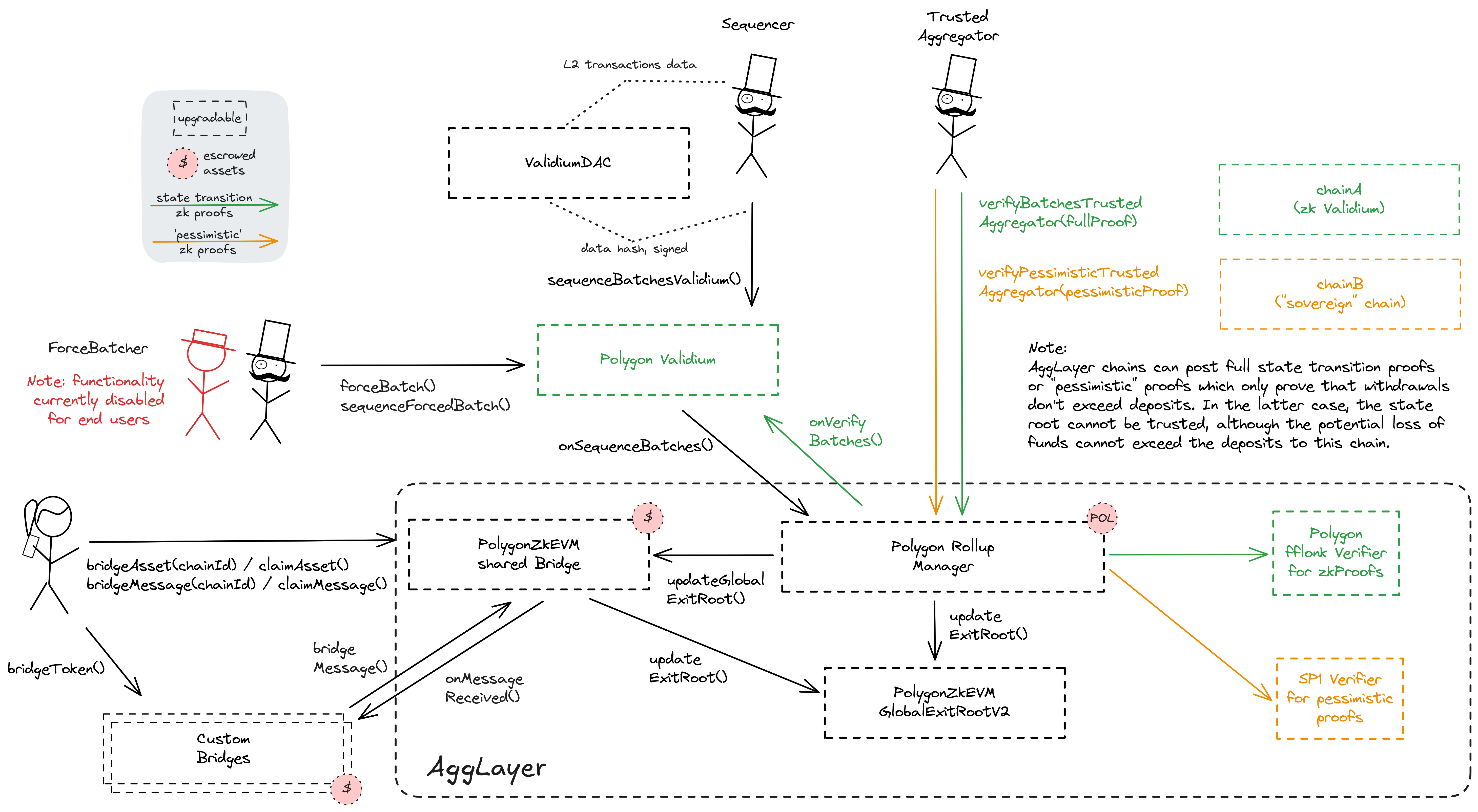
Polygon CDK validiums utilize a data availability solution that relies on a Data Availability Committee (DAC) to ensure data integrity and manage off-chain transaction data. This architecture comprises the following components:
- Operator: A trusted entity that collects transactions, computes hash values for the transaction batch, and then requests and collects signatures from Committee members.
- Data Availability Committee (DAC): A group of nodes responsible for validating batch data against the hash values provided by the operator (sequencer), ensuring the data accurately represents the transactions.
- PolygonCommittee Contract: Contract responsible for managing the data committee members list.
Each DAC node independently validates the batch data, ensuring it matches the received hash values. Upon successful validation, DAC members store the hash values locally and generate signatures endorsing the batch’s integrity. The sequencer collects these signatures and submits the transactions batch hash together with the aggregated signature on Ethereum. The PolygonCommittee contract is used during batch sequencing to verify that the signature posted by the sequencer was signed off by the DAC members stored in the contract.
DA Bridge Architecture

The DA commitments are posted to the destination chain through the sequencer inbox, using the inbox as a DA bridge. The DA commitment consists of a data availability message provided as transaction input, made up of a byte array containing the signatures and all the addresses of the committee in ascending order. The sequencer distributes the data and collects signatures from Committee members offchain. Only the DA message is posted by the sequencer to the destination chain inbox (the DA bridge). A separate contract, the PolygonCommittee contract, is used to manage the committee members list and verify the signatures before accepting the DA commitment.
Funds can be lost if a malicious committee signs a data availability attestation for an unavailable transaction batch.
Funds can be lost if the bridge contract or its dependencies receive a malicious code upgrade. There is no delay on code upgrades.
No compression scheme yet.
The genesis state, whose corresponding root is accessible as Batch 0 root in the getRollupBatchNumToStateRoot method of PolygonRollupManager, is available here.
The trusted sequencer request signatures from DAC members off-chain, and posts hashed batches with signatures to the AstarValidium contract.
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract.
Polygon zkEVM proof system PIL-STARK can be found here.
Polygon zkEVM circuits are built from PIL (polynomial identity language) and are designed to replicate the behavior of the EVM. The source code can be found here.
Funds can be lost if the proof system is implemented incorrectly.
SNARK verification keys can be generated and checked against the Ethereum verifier contract using this guide. The system requires a trusted setup.
The pessimistic proofs that are used to prove correct accounting in the Agglayer shared bridge are using the SP1 zkVM by Succinct.
Each update to the system state must be accompanied by a ZK proof that ensures that the new state was derived by correctly applying a series of valid user transactions to the previous state. These proofs are then verified on Ethereum by a smart contract.
The system has a centralized sequencer
Only a trusted sequencer is allowed to submit transaction batches. A mechanism for users to submit their own batches is currently disabled.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Funds can be frozen if the sequencer refuses to include an exit transaction (CRITICAL).
Users can't force any transaction
The mechanism for allowing users to submit their own transactions is currently disabled.
Users can be censored if the operator refuses to include their transactions.
Shared bridge and Pessimistic Proofs
Polygon Agglayer uses a shared bridge escrow for Rollups, Validiums and external chains that opt in to participate in interoperability. Each participating chain needs to provide zk proofs to access any assets in the shared bridge. In addition to the full execution proofs that are used for the state validation of Rollups and Validiums, accounting proofs over the bridges state (Polygon calls them ‘Pessimistic Proofs’) are used by external chains (‘cdk-sovereign’). Using the SP1 zkVM by Succinct, projects without a full proof system on Ethereum are able to share the bridge with the zkEVM Agglayer projects.
Funds can be lost if the accounting proof system for the bridge (pessimistic proofs, SP1) is implemented incorrectly.
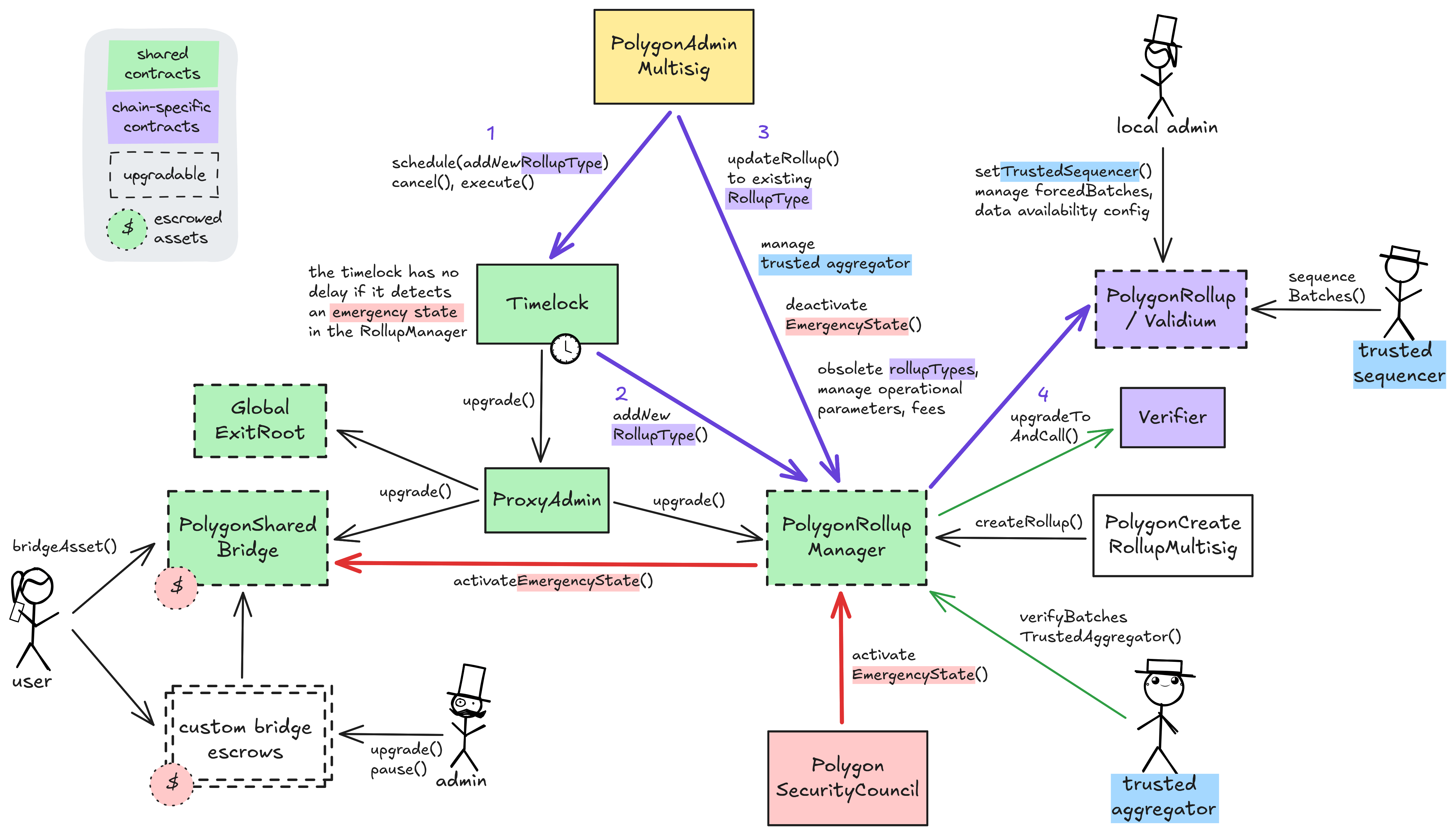
The regular upgrade process for all system contracts (shared and L2-specific) starts at the PolygonAdminMultisig. For the shared contracts, they schedule a transaction that targets the ProxyAdmin via the Timelock, wait for 3d and then execute the upgrade. An upgrade of the Layer 2 specific rollup- or validium contract requires first adding a new rollupType through the Timelock and the RollupManager (defining the new implementation and verifier contracts). Now that the rollupType is created, either the local admin or the PolygonAdminMultisig can immediately upgrade the local system contracts to it.
The PolygonSecurityCouncil can expedite the upgrade process by declaring an emergency state. This state pauses both the shared bridge and the PolygonRollupManager and allows for instant upgrades through the timelock. Accordingly, instant upgrades for all system contracts are possible with the cooperation of the SecurityCouncil. The emergency state has been activated 1 time(s) since inception.
Furthermore, the PolygonAdminMultisig is permissioned to manage the shared trusted aggregator (proposer and prover) for all participating Layer 2s, deactivate the emergency state, obsolete rolupTypes and manage operational parameters and fees in the PolygonRollupManager directly. The local admin of a specific Layer 2 can manage their chain by choosing the trusted sequencer, manage forced batches and set the data availability config. Creating new Layer 2s (of existing rollupType) is outsourced to the PolygonCreateRollupMultisig but can also be done by the PolygonAdminMultisig. Custom non-shared bridge escrows have their custom upgrade admins listed in the permissions section.
Ethereum
Roles:
Allowed to commit transactions from the current layer to the host chain.
Permissioned to post new state roots and global exit roots accompanied by ZK proofs.
Actors:
A Multisig with 5/12 threshold.
- Can upgrade with 3d delay
- AggLayerGateway Timelock with 3d delay (no delay if in emergency state) → SharedProxyAdmin
- PolygonSharedBridge Timelock with 3d delay (no delay if in emergency state) → SharedProxyAdmin
- PolygonRollupManager Timelock with 3d delay (no delay if in emergency state) → SharedProxyAdmin
- PolygonGlobalExitRootV2 Timelock with 3d delay (no delay if in emergency state) → SharedProxyAdmin
- Can interact with AggLayerGateway
- add new routes from proof selector to verifier / pessimisticVkey for pessimistic proofs with 3d delay Timelock with 3d delay (no delay if in emergency state)
- add or update default aggchain verification keys (aggchainVkey) for any given selectors
- freeze routes from proof selector to verifier / pessimisticVkey for pessimistic proofs
- Can interact with PolygonSharedBridge
- upgrade the implementation of wrapped tokens deployed by the bridge with 3d delay Timelock with 3d delay (no delay if in emergency state)
- Can interact with PolygonRollupManager
- deploy new projects that use predefined rollup types (implementations) and connect them or other Agglayer chains to the PolygonRollupManager
- manage all access control roles, add new rollup types (which are implementation contracts that can then be upgraded to by connected projects), update any connected projects to new rollup types, migrate to pessimistic proofs and rollback batches, connect existing rollups to the PolygonRollupManager with 3d delay Timelock with 3d delay (no delay if in emergency state)
- manage parameters like fees for all connected projects, set the trusted aggregator, stop the emergency state, update projects and obsolete rollup types
- Can interact with Timelock
- propose, cancel and execute transactions in the timelock, manage all access control roles and change the minimum delay with 6d delay or with 3d delay Timelock with 3d delay (no delay if in emergency state) with 3d delay (no delay if in emergency state) - or - acting directly with 3d delay (no delay if in emergency state)
Participants (12):
0xcAB3…62f90xAb35…235E0x54c4…65d90x2161…d4170xED7c…B5a20xdFEd…56Da0xffbf…32380xeD44…dB370x516e…46B70x4c16…88910xA0B0…f2270xEad7…9dB2A Multisig with 3/6 threshold.
- Can upgrade with no delay
- PolygonDataCommittee ProxyAdmin
- Can interact with Validium
- set core system parameters like the trusted sequencer and manage forced transactions/batches
- sole address that can force batches
- Can interact with PolygonDataCommittee
- manage the members of the data availability committee and the threshold for valid commitments
A Multisig with 6/8 threshold.
- Can interact with PolygonRollupManager
- activate the emergency state in the PolygonRollupManager and in the shared bridge immediately, effectively pausing all projects connected to them and making system contracts instantly upgradable
Participants (8):
0xFe45…2e4b0xaF46…261D0xBDc2…FEFf0x4c16…88910x3ab9…D6220x49c1…0E860x9F7d…86A00x2188…1C28A Multisig with 3/7 threshold.
- Can interact with PolygonRollupManager
- deploy new projects that use predefined rollup types (implementations) and connect them or other Agglayer chains to the PolygonRollupManager
A Multisig with 1/3 threshold. Member of AstarMultisig.
Ethereum
Verifies ZK proofs for state roots of this Layer 2 via the PolygonRollupManager.
The main system contract defining the Astar zkEVM Layer 2 logic. Entry point for sequencing batches.
- Roles:
- admin: AstarMultisig
- forceBatchAddress: AstarMultisig
- trustedSequencer: EOA 1
Manages the members of the data availability committee (DAC) and the threshold for accepting commitments from them (Currently 5/3).
- Roles:
- admin: ProxyAdmin; ultimately AstarMultisig
- owner: AstarMultisig
A verifier gateway for pessimistic proofs. Manages a map of chains and their verifier keys and is used to route proofs based on the first 4 bytes of proofBytes data in a proof submission. The SP1 verifier is used for all proofs.
- Roles:
- addPpRoute: Timelock; ultimately PolygonAdminMultisig
- admin: SharedProxyAdmin; ultimately PolygonAdminMultisig
- aggchainDefaultVKey: PolygonAdminMultisig
- freezePpRoute: PolygonAdminMultisig
The shared bridge contract, escrowing user funds sent to Agglayer participants. It is usually mirrored on each chain and can be used to transfer both ERC20 assets and arbitrary messages.
- Roles:
- admin: SharedProxyAdmin; ultimately PolygonAdminMultisig
- proxiedTokensManager: Timelock; ultimately PolygonAdminMultisig
- This contract can store any token.
The central shared managing contract for Polygon Agglayer chains. This contract coordinates chain deployments and proof validation. All connected Layer 2s can be globally paused by activating the ‘Emergency State’. This can be done by the PolygonSecurityCouncil or by anyone after 1 week of inactive verifiers.
- Roles:
- admin: SharedProxyAdmin; ultimately PolygonAdminMultisig
- createRollup: PolygonAdminMultisig, PolygonCreateRollupMultisig
- defaultAdmin: Timelock; ultimately PolygonAdminMultisig
- emergencyCouncilAdmin: PolygonSecurityCouncil
- trustedAggregator: EOA 2, EOA 3
- tweakParameters: PolygonAdminMultisig
A merkle tree storage contract aggregating state roots of each participating Layer 2, thus creating a single global merkle root representing the global state of the Agglayer, the ‘global exit root’. The global exit root is synchronized to all connected Layer 2s to help with their interoperability.
- Roles:
- admin: SharedProxyAdmin; ultimately PolygonAdminMultisig
A timelock with access control. In the case of an activated emergency state in the PolygonRollupManager, all transactions through this timelock are immediately executable. The current minimum delay is 3d.
- Roles:
- timelockAdmin: PolygonAdminMultisig (no delay if in emergency state), Timelock (no delay if in emergency state); ultimately PolygonAdminMultisig (no delay if in emergency state)
- Roles:
- owner: AstarMultisig
Value Secured is calculated based on these smart contracts and tokens:
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is a 3d delay on code upgrades unless upgrade is initiated by the PolygonSecurityCouncil in which case there is no delay.